On May 28 of 2021, at 13:37 (following the tradition), the Pwn2Win CTF 2021 began. This year, in addition to our high CTFTime rating (83.41), we received the responsibility of selecting a team for DEFCON CTF Finals, which attracted many world Top Teams and gave us a fierce and exciting dispute. It took us about 6 months to organize it.
This edition broke several records:
- The largest number of registered teams: 1091 (+26%)
- The largest number of scoring teams: 720 (+80%)
- The first Brazilian CTF chosen as DEFCON CTF Qualifier
- The largest sponsorship, both in value and number of partners
Organization Team
In addition to the ELT members, collaborators helped us with challenges and other activities before and during the CTF. We want to thank the folks:
- Álisson “gnx” Bertochi: Coordinator. Miscellaneous challenges author
- André Smaira: Marketing. Coordinator. Reversing and Miscellaneous challenges author
- Caio Lüders: Web Hacking and Miscellaneous challenges author
- Caue Obici: Exploitation and Web Hacking challenges author
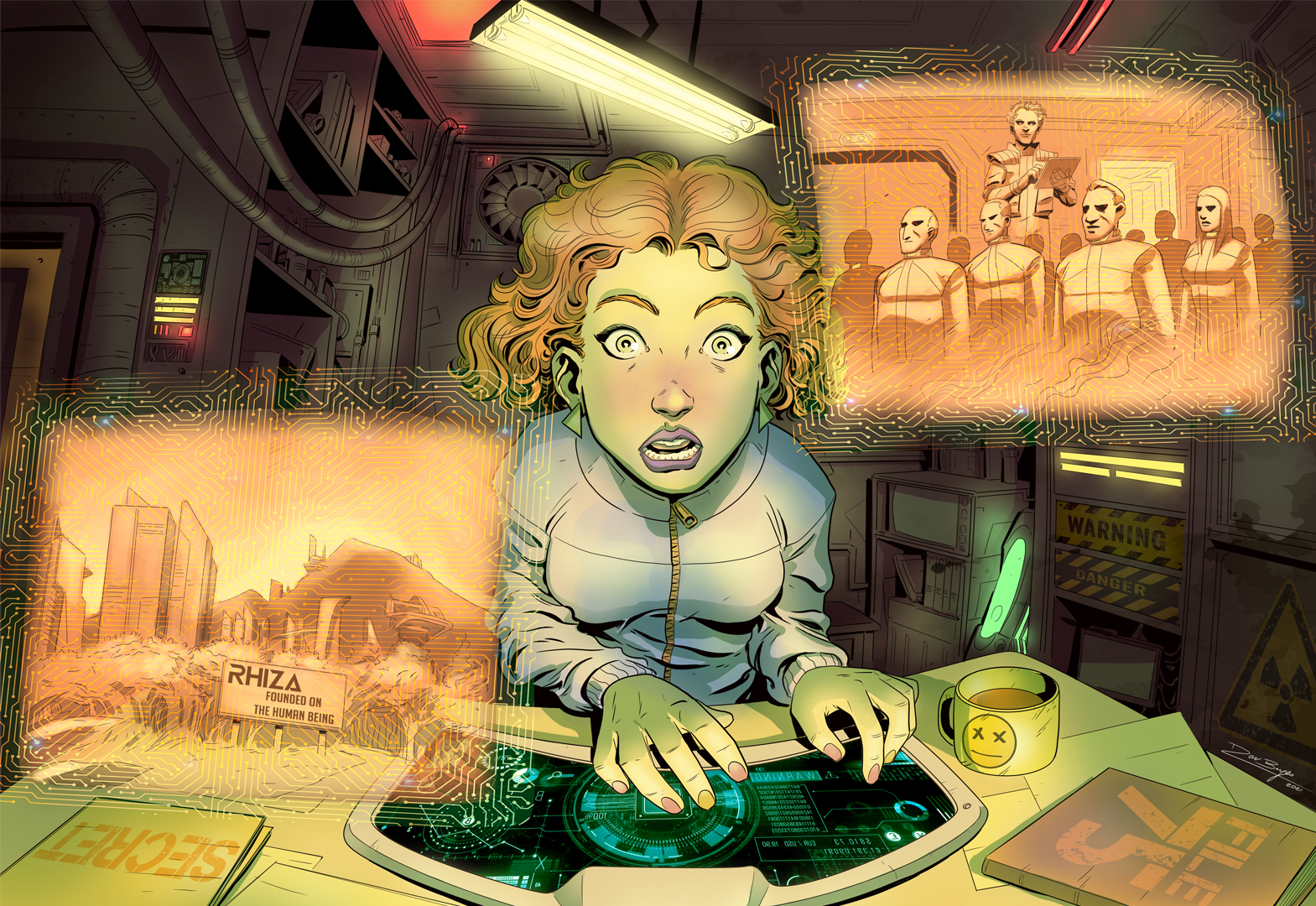
- Dan Borges: Story illustration. We strongly recommend his work, see here.
- Éderson “edstz” Szlachta: Winners certificates maker
- Fernando “feroso” Dantas: Exploitation challenges author
- João “Chinchila” Sobral: Cryptography challenges author
- José “esoj” Luiz: Exploitation challenges author
- Lorhan Sohaky: Web frontend development. Support and hotfixes during the event.
- Luan Herrera: Web Hacking challenges author
- Lucas Teske: Reversing and Hardware challenges author
- Matheus “abrasax” Vrech: Web Hacking challenges author
- Matteus “n0one” Silva: Healthchecker maker and Deployer. Support and hotfixes during the event.
- Mesailde Matias: Story author
- Paulo “thotypous” Matias: Coordinator. Reversing, Hardware and Miscellaneous challenges author. Support and hotfixes during the event.
- Pedro “pedroysb” Barbosa: Cryptography and Exploitation challenges author. Support and hotfixes during the event.
- Saullo “n0ps13d” Carvalho: Exploitation and Reversing challenges author
- Thales “c4v0k” Araújo: Cryptography challenges author
- Vinicius “pdpano” Aurichio: Story translator
It was not so easy
After the CTF, we could have said it was easy to make the Pwn2Win happen, but it wasn’t. There were many challenges in the Pwn2Win organization besides the ones that the players had to solve!
People
This is always the most stressful challenge. Making Pwn2Win took months and much work from volunteers that made it happen just for the pleasure of doing it. We used some tools to manage it, like:
GitLab: challenges version control (Infos, Attachments and Deploy), checklists, and issues (challenges ideas). The following video shows the interactions of people with the repository
Google Calendar: deadline dates
Google Meet: important decisions and development monitoring meetings.
Google Sheets: challenges making status control.

Google App Script: automatic reminder emails.

Telegram: main organization communication channel.
Infrastructure
Like last year, we got Sponsored by Google and had $700 in GCP credits to use. Here are some of the technologies we used in this record-breaking edition:
CloudFlare: platform protection, some Web Challenges SSL and DNS server for challenges:

Docker: containers technology used in the challenges deploys.
DreamHost: main challenges files repository
Google Drive: mirror challenges files repository
GitHub: challenges description and information repository host
Google Cloud Platform: challenges VMs (one per challenge), Firebase (Realtime Database) and the LoadBalance feature for some challenges.
Grafana: challenges health checker. The Healthchecker was a python script running all the challenges solvers and providing a JSON with each challenge status, which was received and used by Grafana for charts generation.

Good Challenges
Innovation is at the core of every pwn2win. We have always prepared very unique challenges and this is a very important feature for us! Keeping the already known and expected quality, as well as honor our high CTFTime rating, are very difficult tasks. Our 0days and innovative challenges were only possible again due to months of the full dedication of our wonderful team members.
Ranking
Due to our high rating and the DEFCON CTF spot, the world’s top team played Pwn2Win 2021. The dispute was intense! There were many overtakings, which made this historic edition even more fantastic. There were 1094 registered teams (+26% increase over Pwn2Win 2020), and 720 scoring teams (+80% increase over our previous record).
Towards the end of the event, we had one more surprise when the DiceGang team submitted many flags sequentially, which were being hidden to surprise the other teams at the end, a practice known as “flag hoarding”. For sure everyone was surprised! This technique is controversial in relation to fair play, but not forbidden by any rules.

In end, the winners were DiceGang (USA), uuunderflow (KOR+JAP) e justCatTheFish (POL). They solved many difficult challenges and we congratulate them on this!

Ranking of Brazilian teams
The top 3 Brazilian teams are:
1º (18º overall) Ganesh – Team of ICMC (Institute of Math and Computational Sciences) from USP (University of São Paulo).
2º (36º overall) FireShell
3º (44º overall) Shingeki No Covid – Team of UFSCar (University of São Carlos) students.
Congratulations!

Pwn2Win 2021 in numbers
- Registered teams: 1094
- Scoring teams: 720
- Teams X Time:

Registered teams by country
- Registered countries: 94
- Top number of registered teams:
- IND – 147
- BRA – 124
- USA – 122
- CHN – 55
- KOR – 49
- Top number of scoring teams:
- IND – 90
- USA – 88
- BRA – 58
- JPN – 36
- KOR – 35
- Top maximum scores:
- USA – 6819
- KOR / JPN – 5808
- POL – 4385
- DNK – 4011
- CHN – 3870
- Top average scores:
- HKG – 2705
- KAZ – 1097
- COG – 1093
- DNK – 1015
- POL – 704
Correct submissions
- Total: 1114
- Solves per hour

Solves rate
- Maximum: 1 solve each 1.3043 seconds at CTF beggining
- Average: 1 solve each 155.1167 seconds
- Minimum: 1 solve each 2640 seconds, 6 hours before CTF ended
Challenges
- Number of challenges: 27
- Each challenge:
- [bonus] Rhiza – founded on the human being: 714 solves, by mesailde
- [crypto] A2S: 10 solves, by c4v0k
- [pwn] Accessing the Truth: 8 solves, by pedroysb
- [pwn] Baby write-only password manager: 20 solves, by esoj
- [misc] Botnet – The Final Bypass: 4 solves, gnx
- [pwn] C’mon See my Vulns: 54 solves, by caue
- [crypto] cladorhizidae: 12 solves, by c4v0k
- [misc] Dots Exposed: 33 solves, by caioluders
- [pwn] Enlighten Me Pt.1: 7 solves, by feroso
- [pwn] Enlighten Me Pt.2: 0 solves, by feroso
- [web] HackUs: 10 solves, by herrera
- [rev] Highest Power: 1 solve, by n0ps13d
- [web] Illusion: 78 solves, by caue
- [crypto] Kangurei: 3 solves, by chinchila
- [misc] Lost Exponent: 31 solves, by andre_smaira
- [web] MessageKeeper: 2 solves, by herrera
- [crypto] Oh, Anna Julia: 49 solves, by pedroysb
- [misc] Oldschool Adventures – Apple II: 11 solves, by gnx
- [pwn] pe_analysis: 3 solves, by n0ps13d
- [web, misc] Ruthless Monster: 13 solves, by caioluders
- [web] Small Talk: 16 solves, by vrech
- [crypto] t00 rare: 13 solves, by pedroysb
- [hardware, rev] The ethernet from above: 0 solves, by racerxdl and thotypous
- [hardware, rev] The REAL ethernet from above: 0 solves, by racerxdl and thotypous
- [rev] The Return of Too Slow: 16 solves, by andre_smaira and thotypous
- [pwn] True write-only password manager: 5 solves, by esoj
- [misc] WSPR decoy: 1 solve, by thotypous
After the end
After Pwn2Win 2021 ended, we announced that the challenge The ethernet from above would have an extra prize if solved within one week since it had no solution during event time. It happened and we congratulate Maple Bacon by it. This and all of the other PWn2Win CTF challenges Write-Ups can be found here.
Acknowledgments
In addition to all ELT members, who did more than the possible to make this Pwn2Win 2021 be the success it was, we thank all our friends that help us, mainly Lorhan, who worked hard in this excellent game platform.
Furthermore, we thank our sponsors:
- Google for Infrastructure Sponsorship, essencial for the event
- BugHunt
- PRIDE Security
- Resh Cyber Defense
Final words
One more Pwn2Win and one more year of records! We managed to do an extremely high level extremely original CTF again, with many challenges making history! Top teams’ registrations and very high future rating (99.41, the fourth-highest for 2022 until now) made us sure we made a fantastic Pwn2Win again! We will continue improving based on players’ feedbacks and bring an even more perfect event next year with Pwn2Win 2022! Wait for us!